Microsoft has released patches for two new zero-day vulnerabilities in Microsoft Exchange, CVE-2022-41040 and CVE-2022-41082 but researchers warn that the on-premises server mitigation is insufficient.
Both of these zero-day vulnerabilities are already being chained together in real-world attacks against Microsoft Exchange servers to gain remote code execution.
About three weeks ago, Vietnamese cybersecurity firm GTSC reported both vulnerabilities privately through the Zero Day Initiative program; they only recently made their disclosure public.
Mitigation Is Overly Specific
On Friday, Microsoft acknowledged the two vulnerabilities and said they were “aware of limited targeted attacks” that took advantage of them. Microsoft included mitigations for on-premises servers and a strong recommendation for Exchange Server customers to “disable remote PowerShell access for non-admin users in the organization” in an advisory.
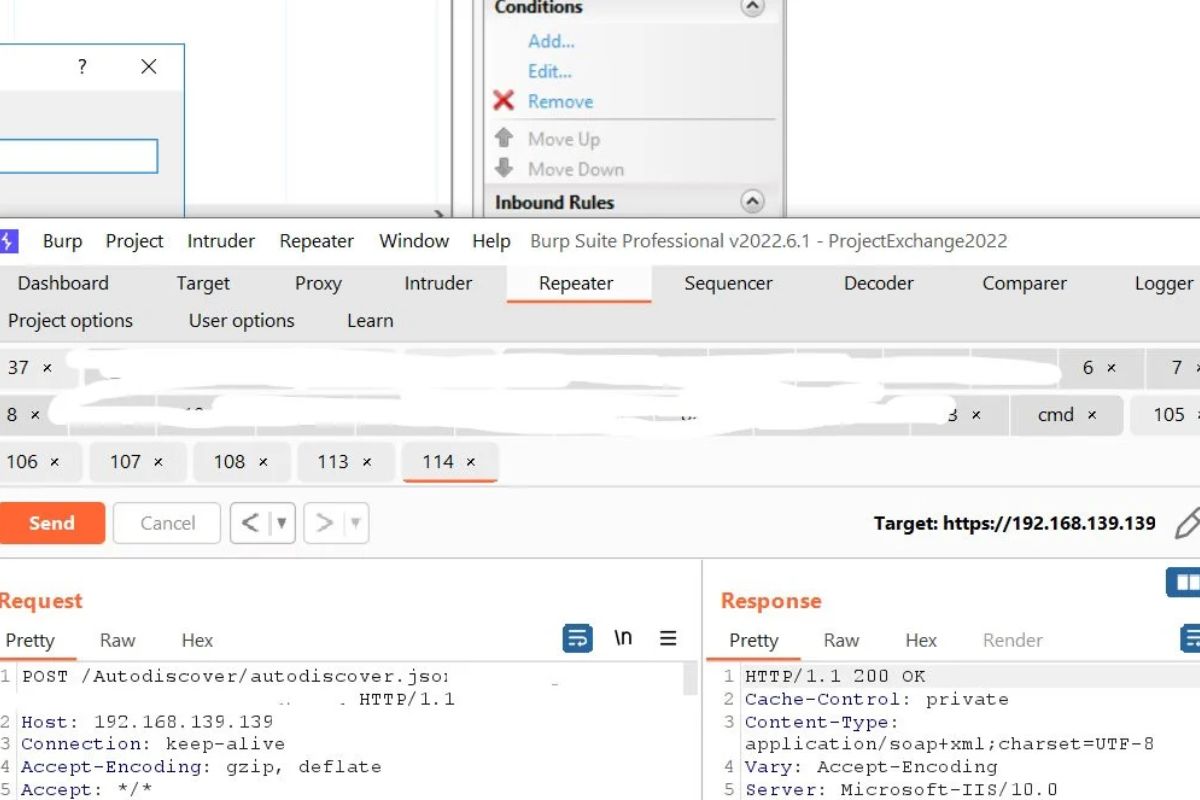
Microsoft suggested implementing a rule in IIS Manager to block the known attack patterns which would significantly lower the potential for exploitation.
- Open the IIS Manager.
- Select Default Web Site.
- In the** Feature View**, click URL Rewrite.
- In the Actions pane on the right-hand side, click Add Rules…
- Select** Request Blocking** and click OK.
- Add the string “.autodiscover.json.*@.*Powershell.” (excluding quotes) and then click OK.
- Expand the rule and select the rule with the pattern “auto-discover.json.*@.*Powershell.” and click Edit under Conditions.
- Change the Condition input from {URL} to {REQUEST_URI}
Alternatively, administrators can get the same result by executing the latest version of Microsoft’s Exchange On-premises Mitigation Tool, a script that calls for PowerShell 3 or later needs to run with admin privileges and runs on IIS 7.5 or later.
However, the Microsoft-proposed rule covers only known attacks, so the URL pattern is restricted to those. In a tweet published today, security researcher Jang demonstrates how easy it is to circumvent Microsoft’s temporary fix for CVE-2022-41040 and CVE-2022-41082.
You Can Also Read
Five New Apple Products Could Launch In 2023
Why Apple Banned Instagram’s Ad-Free Version
According to ANALYGENCE’s senior vulnerability analyst Will Dormann, the ‘@’ in Microsoft’s URL block “seems unnecessarily precise, and therefore insufficient.” Researchers at GTSC have verified Jang’s discovery, stating in a video released today that Microsoft’s mitigation does not offer adequate security.
Jang proposed a more generalized solution to the problem than Microsoft’s proposed URL block:
.*autodiscover\.json.*Powershell.*Hybrid deployments Are At Risk
Microsoft has stated in their advisories for these two vulnerabilities that Exchange Online users are exempt from taking any remedial action while on-premises Exchange Server users must follow the provided mitigation instructions.
Many businesses, however, use both on-premises and cloud deployment of Microsoft Exchange making them equally susceptible. Today, security researcher Kevin Beaumont released a video in which he warned that any company using an on-premise Exchange Server deployment was inviting danger.
Businesses with a hybrid Exchange setup need to think about the risk they’re exposed to, according to Beaumont, who calls the exploit chain ProxyNotShell.
More than 1,200 of these companies also make public their hybrid infrastructure. Financial institutions, universities and government agencies are all prime targets for cybercriminals engaged in espionage or blackmail.
A Patch Is On Its Way
As of this writing, Microsoft has not issued a patch for either vulnerability but the company has issued security advisories detailing the issues’ effects and the steps needed to exploit them.
According to Microsoft, CVE-2022-41040 is a critical flaw with a severity rating of 8.8 out of 10 that allows an attacker to gain elevated privileges on a vulnerable system without the user’s knowledge or consent.
The lack of a higher severity rating for this security issue is due to the necessity of authenticating the threat actor.
Attackers with “privileges that provide basic user capabilities” can exploit CVE-2022-41082, another vulnerability with a similar high severity rating, to remotely execute code on vulnerable on-premise Microsoft Exchange Servers (settings and files owned by the user).
Stay tuned for more updates at nogmagazine.com.