Two zero-day vulnerabilities in Microsoft Exchange Server are being actively targeted and a patch is currently in development. GTSC, a Vietnamese cybersecurity company discovered the two vulnerabilities in Microsoft’s enterprise mail server and assigned the identifiers CVE-2022-41040 and CVE-2022-41082.
This issue affects on-premises Microsoft Exchange Server 2013, 2016 and 2019 and Microsoft has said it is aware of “a small number of targeted attacks” that exploit it. The authentication to PowerShell requirement makes these flaws appear to be less severe variants of the critical ProxyShell vulnerabilities that were exploited extensively in 2021.
RCE Chain
An attack on “critical” infrastructure using Exchange Server was reported in August by researchers, according to the original security advisory published by GTSC.
Server-side request forgery (SSRF) is the first vulnerability identified as CVE-2022-41040 (CVSS 8.8). CVE-2022-41082 (CVSS 6.3) could allow for remote code execution if triggered from a remote location (RCE). However, proof-of-concept (POC) code is expected to appear soon because the vulnerabilities have not yet been patched and full technical details have not been released.
Following its investigation, GTSC shared its findings with Trend Micro’s Zero Day Initiative (ZDI). The ZDI team confirmed the vulnerabilities and contacted Microsoft’s Security Response Center (MSRC) which then confirmed the report and published an analysis of attacks that took advantage of them.
The two vulnerabilities are independent of one another but Microsoft stressed that “authenticated access to the vulnerable Exchange Server is necessary” for exploiting them. Unfortunately, it only requires a simple user account to access. Theft, credential stuffing and brute-force attacks are all ways in which cybercriminals can obtain such credentials.
State-Sponsored Attacks
Microsoft claims that a “state-sponsored organization” has attacked fewer than 10 organizations worldwide. GTSC researchers said there are indicators that a Chinese threat group is leveraging Antsword, a Chinese cross-platform website management suite with web shell functionality.
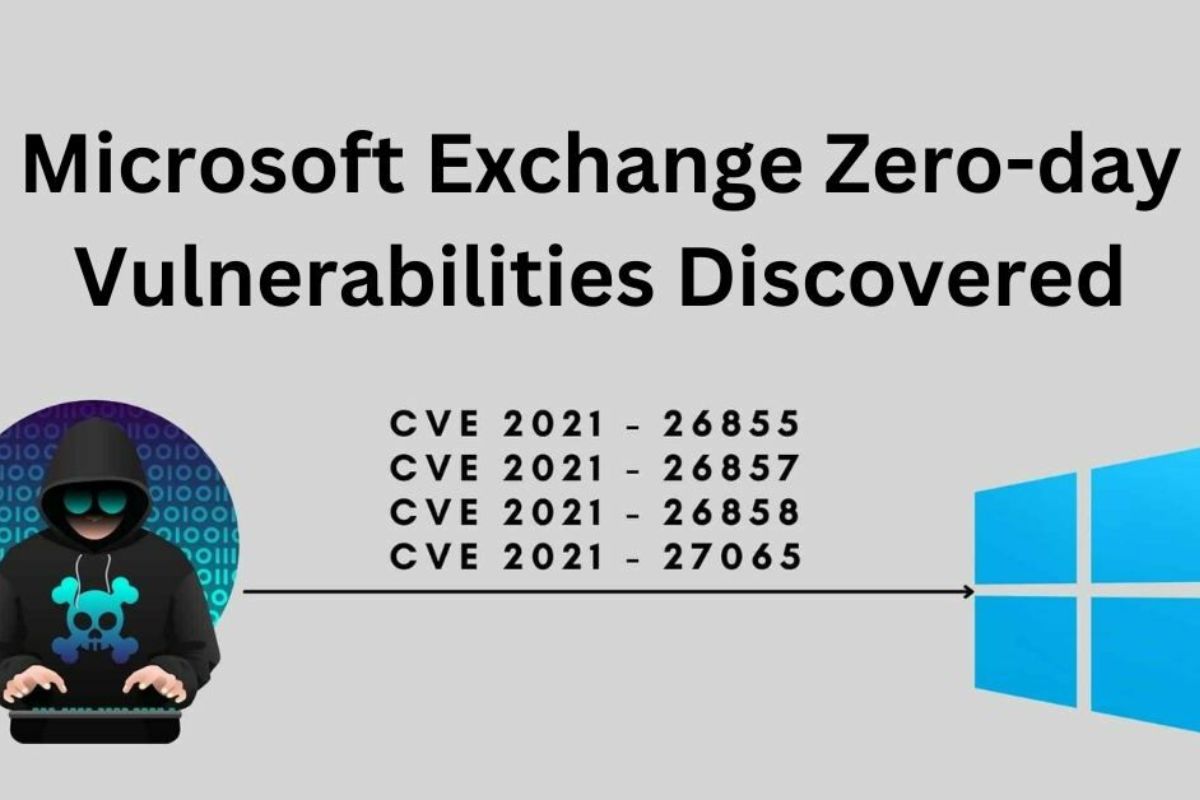
It appears that reconnaissance and data exfiltration were performed on Active Directory using the web shell China Chopper. If this sounds familiar, it’s because, in 2021, attackers used the same web shell to exploit zero-day vulnerabilities in Exchange Server. The Chinese state-backed hacking group HAFNIUM has been blamed for these attacks.
Kevin Beaumont, a security researcher has noticed that the new bugs which he has dubbed “ProxyNotShell,” follow a similar trajectory to the zero-day exploits from 2016.
The original ProxyShell flaws were discovered by Devcore researcher Orange Tsai, who also predicted that new variants would appear due to fundamental path confusion issues in a talk given at last year’s Black Hat USA.
Mitigation Advice
Microsoft has issued advice to customers on how to deal with the new bugs in the absence of a patch. The business strongly suggests that customers immediately stop allowing non-administrators remote access to PowerShell. Additional safeguards will be implemented mechanically once the Exchange Emergency Mitigation Service (EEMS) is activated.
The technology company claims that Exchange Online users can relax. This statement has been questioned by Beaumont, who points out that migrating to Microsoft Exchange Online necessitates the use of hybrid, publicly accessible Exchange servers on the internet.
Microsoft noted that as “similar threats and overall exploitation of these vulnerabilities” rise as security researchers and cybercriminals incorporate the published research into their toolkits and proof of concept code becomes available, the company is not surprised. The two zero days have been added to CISA’s Known Exploited Vulnerabilities Catalog.